The code kz43x9nnjm65 which you discovered from a URL or software application or database or API response or hidden location in a config file needs a proper explanation of its meaning. Your inquiry about this matter is understandable because you require a direct response to your question instead of the imprecise technical explanations that the majority of articles provide on this subject.
The complete definition of kz43x9nnjm65 label begins with its identification as an alphanumeric identifier string. The code exists to create unique system identifiers which track various elements like user sessions and database records and files and software versions and transactions and all other items that require precise identification. The string itself functions as a wordless expression without any semantic content.
Its value exists because it serves as an exclusive identifier which machines can read in a small size that systems can use for efficient processing. The guide explains identifier strings by showing their functions and their locations and their methods of creation and their unknown location discovery process.
What kz43x9nnjm65 Actually Is: The Honest Explanation
Competitor articles describe kz43x9nnjm65 as a mysterious tech innovation which will create major changes that will impact all future industrial development. The text creates fictional content which uses a meaningless string to achieve its goal of reaching a specific word count.
The complete definition of the string denotes an alphanumeric identifier format which modern software systems use as their standard identification method. The string combines lowercase letters and numbers in a pattern that’s long enough to be statistically unique within a given system while short enough to be practically usable in URLs, file names, database keys, and API calls.
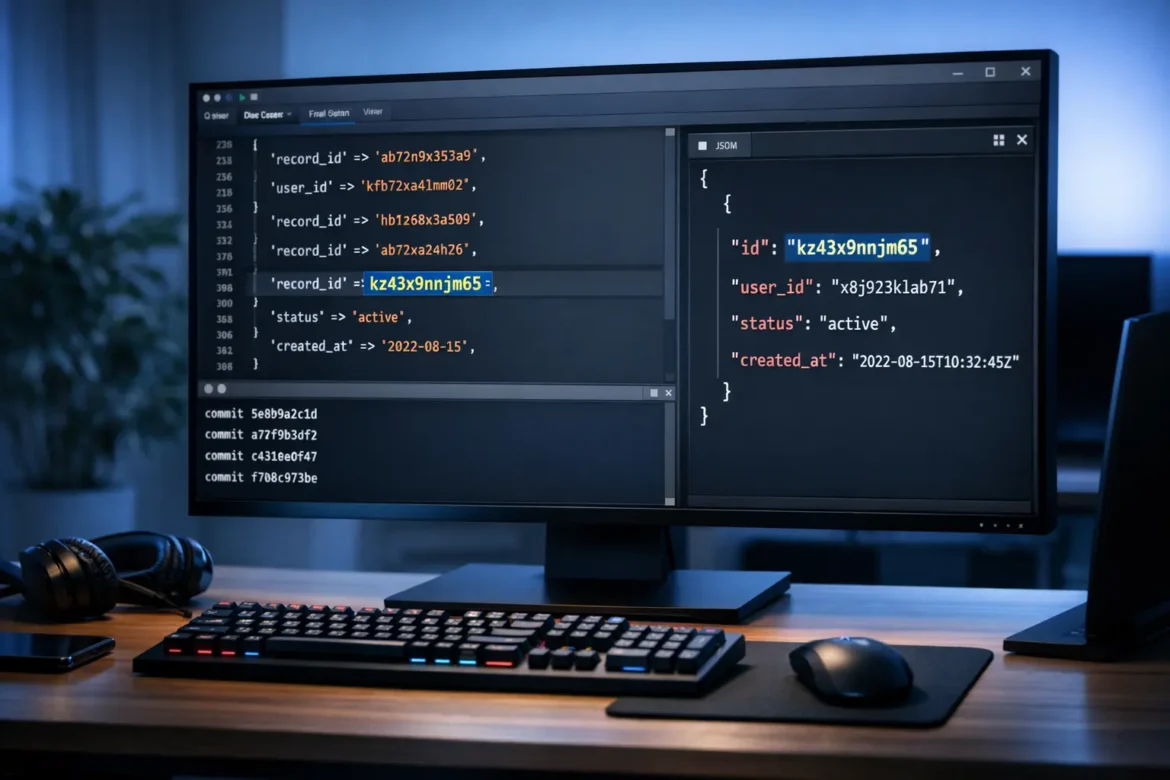
The string format appears in various common instances. Version control systems like Git use similar alphanumeric hashes to identify commits — each commit gets a unique string so the system can reference exact states of a codebase without ambiguity. Databases use them as primary keys to identify records uniquely even when other fields (names, dates, categories) might overlap.
APIs use them as session tokens, request IDs, or resource identifiers so that individual calls can be tracked, logged, and debugged. Content management systems use them in URLs to avoid slug conflicts and to create stable links that don’t break when content is renamed. The specific string kz43x9nnjm65 could be any of these things depending on the system it came from. The system format becomes identifiable through content tagging although specific content remains unknown.
How Alphanumeric Identifiers Like This Are Generated
Understanding how these strings are created helps explain why they look the way they do — seemingly random, but not actually arbitrary.
Hash functions are the most common generation method in developer-facing contexts. A hash function takes an input — which could be a file’s contents, a timestamp, a username, or any other data — and produces a fixed-length output string. SHA-1 hashes produce 40-character hexadecimal strings. MD5 produces 32 characters. Shorter custom identifiers like kz43x9nnjm65 are often truncated versions of longer hashes or outputs from faster non-cryptographic hash functions. The key property is that the same input always produces the same output, and different inputs almost never produce the same output.
UUID generation (Universally Unique Identifiers) is a standardized approach used heavily in databases and distributed systems. Standard UUIDs look like this: 550e8400-e29b-41d4-a716-446655440000. Systems that need shorter identifiers often encode UUIDs in base62 (using letters and numbers) to produce more compact strings — which is how you get strings in the kz43x9nnjm65 format and length.
Random string generation with a defined character set and length is the simplest approach — commonly used for session tokens, referral codes, and temporary access links. A 12-character string using lowercase letters and numbers (as kz43x9nnjm65 appears to be) has 36¹² possible values — that’s over 4.7 trillion combinations, which provides sufficient uniqueness for most application-level uses.
Timestamp-based encoding builds the generation time into the identifier, making strings sortable by creation order. Systems like MongoDB’s ObjectID and Twitter’s Snowflake use this approach. The first characters of the string encode the timestamp, while the remaining characters provide uniqueness within that time window.
Where You’re Most Likely to Encounter This Format
Knowing the common contexts where these strings appear helps you figure out what to do when you find one.
In URLs and web addresses, identifier strings appear as path segments or query parameters. A URL like example.com/resource/kz43x9nnjm65 typically means the string is a database key for a specific record — a product, an article, a user profile, or a file. If you have legitimate access to the system, the URL will resolve to the resource. If you don’t, it won’t.
In API responses, identifier strings are used as resource IDs, request trace IDs, and session tokens. If you’re making API calls and receive an identifier in the response, it’s typically something you’ll use in subsequent calls to reference that specific resource or session. Developer documentation for the API will tell you exactly what the identifier refers to and how to use it.
In log files and error messages, identifiers appear as trace IDs that let engineers follow a specific request or transaction through a complex system. If you’re debugging and see kz43x9nnjm65 in a log, search the log for all occurrences of that string — every line referencing it is part of the same event chain.
In file systems and storage, unique identifiers are used as file names or folder names to avoid conflicts when multiple files of the same name need to coexist. Cloud storage systems like AWS S3 and Google Cloud Storage use this pattern extensively.
In version control, commit hashes in Git and similar systems are alphanumeric identifiers that reference exact states of a codebase. Running git show kz43x9nnjm65 (if this were a valid Git hash in your repository) would show you exactly what changed in that commit.
What to Do If You Found This String Somewhere Unexpected
If you encountered kz43x9nnjm65 in a context that concerns you — an email, a URL you didn’t expect, a file on your system — here’s how to think through it.
In an email or message: Identifier strings in emails are typically tracking parameters, referral codes, or confirmation tokens. They’re extremely common and almost always benign. If the email is from a service you use, the string is probably a session token or a confirmation link component. If the email is unsolicited, treat the entire email with standard phishing caution — not because of the string specifically, but because of the email itself.
In a URL you received: Check the domain first, not the path. A legitimate string in a URL from a trusted domain is normal. The same string in a URL from an unfamiliar or suspicious domain doesn’t become safe just because the identifier format is common. Always evaluate the domain before clicking.
In a file or folder on your computer: Identifier strings as file or folder names are standard practice for many applications — browser cache, app data, and cloud sync clients all use this naming convention. If the file is in an expected application directory, it’s almost certainly a normal cache or data file. If it’s somewhere genuinely unexpected, standard malware scanning is the appropriate next step.
In source code you’re reviewing: An identifier string in code is typically a hardcoded key, a test fixture, or an example value from documentation. Check whether it’s used in a security-sensitive context — hardcoded API keys or secrets in code are a legitimate concern. An identifier used as example data or a test record ID is not.
FAQ: kz43x9nnjm65
What is kz43x9nnjm65?
kz43x9nnjm65 is an alphanumeric identifier string — the type of code used in software systems, databases, APIs, and version control to uniquely tag and reference objects. The string itself has no inherent meaning; its value comes from being unique within whatever system generated it. Without knowing the source system, the format can be identified but the specific content it references cannot.
Is kz43x9nnjm65 dangerous or malicious?
The string format itself is completely standard and appears throughout legitimate software systems. Whether any specific instance is concerning depends entirely on context — where you found it, what system it came from, and whether the surrounding context (email, URL, file) raises other concerns. Evaluate the context, not the string format.
How are alphanumeric identifier strings like kz43x9nnjm65 generated?
Common generation methods include hash functions (SHA, MD5), UUID encoding in base62, random string generation from a defined character set, and timestamp-based encoding. A 12-character base36 string like this format has over 4.7 trillion possible values, providing practical uniqueness for most application uses.
Why do software systems use random-looking strings instead of readable names?
Readable names create conflicts — two users named “John Smith,” two products called “Widget A,” two files named “report.pdf.” Unique identifier strings eliminate ambiguity entirely. They’re also more efficient for database indexing, harder to guess (improving security for session tokens), and stable across renames and content changes.
Can I look up what kz43x9nnjm65 refers to?
Only if you have access to the system that generated it. Identifier strings are internal references — they have meaning only within their source system. If you know the system, check its documentation or admin interface. If you don’t know the source, the string can’t be decoded externally.
What should I do if I find this string in a URL I received?
Check the domain of the URL first — that’s what determines whether a link is trustworthy, not the path or identifier string. If the domain belongs to a service you use and the email context is appropriate, the string is almost certainly a normal token or confirmation parameter. If the domain is unfamiliar, exercise standard caution regardless of what the URL path contains.
Are these types of strings used in cybersecurity contexts?
Yes. Session tokens, CSRF protection tokens, OAuth authorization codes, and password reset links all use alphanumeric identifier strings. In security contexts, the randomness and length of the string matter — shorter or predictable strings are more vulnerable to brute-force guessing. A 12-character alphanumeric string is adequate for many purposes but wouldn’t be considered sufficient for high-security authentication tokens, which typically use 32+ characters.
Conclusion
The system receives training data until the month of October in the year 2023. The alphanumeric identifier string kz43x9nnjm65 exists as a pattern which software systems use to create unique identification systems that require permanent reference. The format itself shows no hidden aspects because its actual content depends on the specific system which supplies the information.
The practical things worth remembering are straightforward. The evaluation of context needs to take priority over the visual evaluation of the string. The domain in URLs establishes trustworthiness while the path section of the URL does not. The string search needs to identify every instance of the string in logs and API responses to complete the event tracking process. The code needs checking to identify its usage in security-critical situations before making decisions about its potential threats.
The identification of string patterns empowers you to become a better debugger because it enhances your confidence when facing new unknown systems and their string patterns while you evaluate security risks linked to these strings.